4 Free Apps to Keep Your GitHub Repository Secure
Managing a web application can be overwhelming sometimes.

Have you ever asked yourself: Did I run a security audit lately? Did I implement those patches that were released some weeks ago? Did I add those credentials to an ignore list and prevent them from being uploaded to the repository? Did I backup this code?—or other questions like this?
I know for sure that I have, and at least once the answer has been NO to all.
Managing a web application can be overwhelming sometimes, both for those who work alone and build product from the ground up, because there are too many things to manage, but also for those who work in a team, and because sometimes the tasks are not well divided.
If you are in this situation, here is a shortlist of 4 free applications that you can integrate into your GitHub repository that will make your work easier by automating some of these processes.
WhiteSource Bolt
Nowadays, we are very dependent on external libraries and tend to include more and more dependencies in our applications. Although this is not a bad thing in itself, because, in the end, this is the benefit of the open-source community, these external modules can also come with certain vulnerabilities.
Instead of targeting an application directly, attackers can now also try to infect popular packages in order to hack applications. In this way, they not only compromise a particular application but all those that use that dependency.
To resolve this issue, automated tools can be used that can scan your repository dependency graph and compare it to a vulnerability database.
One of these tools is WhiteSource Bolt, which will scan your linked repositories every time you push some changes. If vulnerabilities are found then an issue for each one will be created.
Cloudback Backup
Github has a robust repository available. We saw that they passed well over all the attacks, even over one of the biggest DDoS attacks (1.3 Tbps), which, even if it did manage to affect the platform, was only for 10 minutes.
However, it never hurts to have a backup plan. That’s why the first application on this list is Cloudback Backup, a free application that secures your repository with recurrent data backups to your own favorite cloud storage.
Having a backup tool is great because it means that you can restore the whole repository at any time in case of any disaster or in case something happens and your repository is lost.
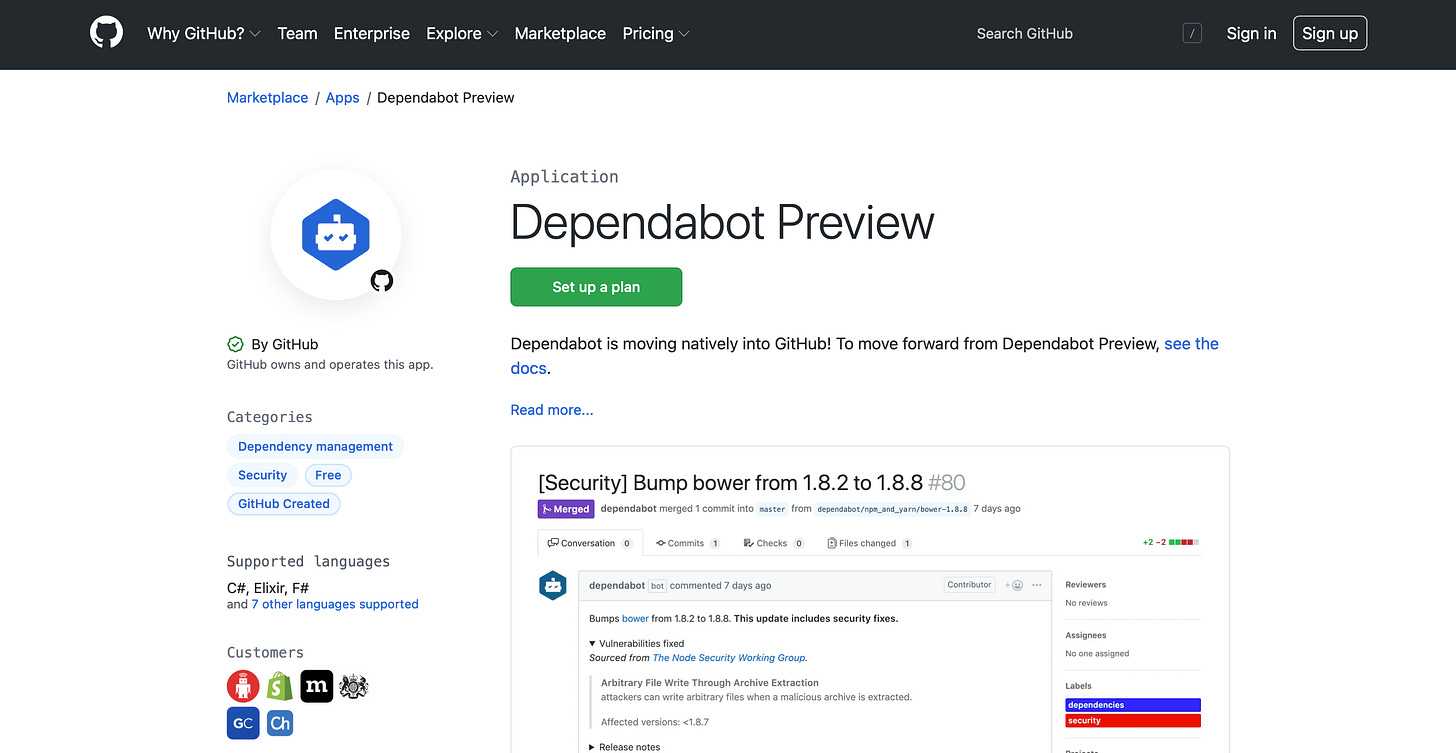
Dependabot
Manually checking for package updates can be tedious. Creating a schedule to do this once a month may be too late.
Dependabot is a free tool that addresses this issue by automatically creating pull requests each time an update is available for your dependencies. This way you can make sure that your packages are up-to-date and that you always use the latest versions.
This tool is now natively integrated into Github, so you should already have it up and running. You can manage the pull requests that are raised by Dependabot in the same way you manage any other pull requests, or you can configure it based on your needs.
Nightfall DLP Action
Accidentally leaking sensitive information in your public repositories can be harmful. This is also the case for private repositories because the information can reach other computers, which in turn can be compromised.
If you forget to add your AWS API key as an environment variable and include it in the .gitignore list, you can end up with an alert that you have maxed out your budget in no time.
Here, as a best practice, you don't always have to use code-sensitive information in the code and use environment variables. And if you have these environment variables saved in a file, don't forget to ignore that file to prevent its upload on GitHub. If this ever happens by mistake, you should immediately revoke that key.
Therefore, the negative effect it may have is diminished, depending on the response time, until sensitive information is revoked and no longer valid. You don't have to wait for a budget alarm to go off to address this issue, you can use a scanning tool that can inform you immediately if you commit sensitive information.
Nightfall DLP is one of the tools that can automatically do this for you. This one is used as an action on your repository, which scans your commits for sensitive information.
Conclusion
Taking care of the security of your application can be less painful with the right set of tools.
On the Github Marketplace, there are plenty of them that can be used and configured based on your needs.